Danlaw delivers exceptional value in automotive cybersecurity services. Let’s get started!
Danlaw delivers exceptional value in automotive cybersecurity services. Let’s get started!
Danlaw delivers exceptional value in automotive embedded software solutions. Let’s get started!
ISO 21434 specifies the framework to deploy cybersecurity across automotive products. It prescribes the methods and measures for validating components to the required cybersecurity assurance levels (CALs). Danlaw can help you define, plan, and execute the testing activities required to achieve your CAL and help you ensure your component, system or application is protected and conforms to ISO 21434 requirements.
Danlaw uses the methods in the following table to ensure you meet ISO 21434 cybersecurity assurance levels.
| Testing Methods | CAL1 | CAL2 | CAL3 | CAL4 |
|---|---|---|---|---|
| Fuzz Testing | X | X | X | X |
| Black Box Penetration Testing | X | X | ||
| White Box Penetration Testing | X | X |
Note 1: Black box pen testing uses publicly known information about the target, limited time and expertise, and uses off-the-shelf equipment to perform the testing.
Note 2: White box pen testing uses enhanced information about the target, such as source code, network configuration, operating system's details, etc.
A penetration test is an authorized simulated cyberattack on a computer system, performed to evaluate the security of the system, and is intended to identify vulnerabilities), including the potential for unauthorized parties to gain access to the system’s features and data.
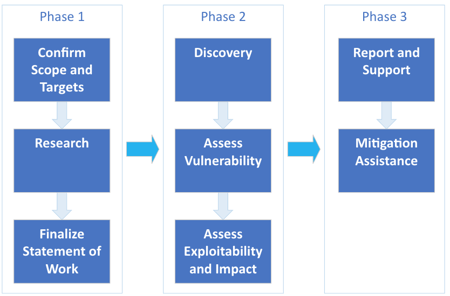
Danlaw conducts a three-phase process to plan to execute the penetration testing: A statement of work is jointly developed between the client and Danlaw, based on what the component, system, and applications provide to the vehicle and users.
Fuzzing or fuzz testing is an automated software testing technique that involves providing invalid, unexpected, or random data as inputs to a computer program. The program is then monitored for exceptions such as crashes, failing built-in code assertions, or potential memory leaks.
Most Automotive OEMs mandate fuzz testing for all ECUs connected to vehicle buses like CAN and Ethernet, as well as other interface such as NFC or Bluetooth. They typically specify the interfaces, protocols, the test setup, and how many cycles should be executed. Danlaw has standardized these tests to support most OEMs.
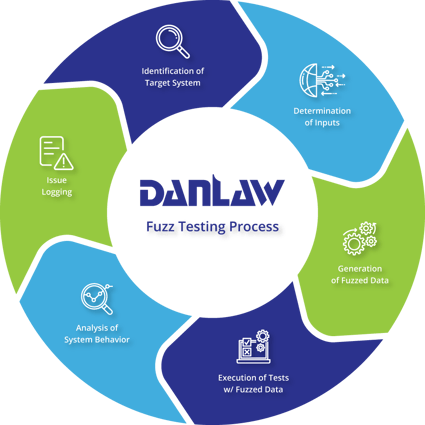
Comprehensive Fuzz Tests
Complete Test Report Documentation
Test Bulletins Upon Discovery of Issues
Not sure what you need? Contact us for a free consultation.